- TRENDING
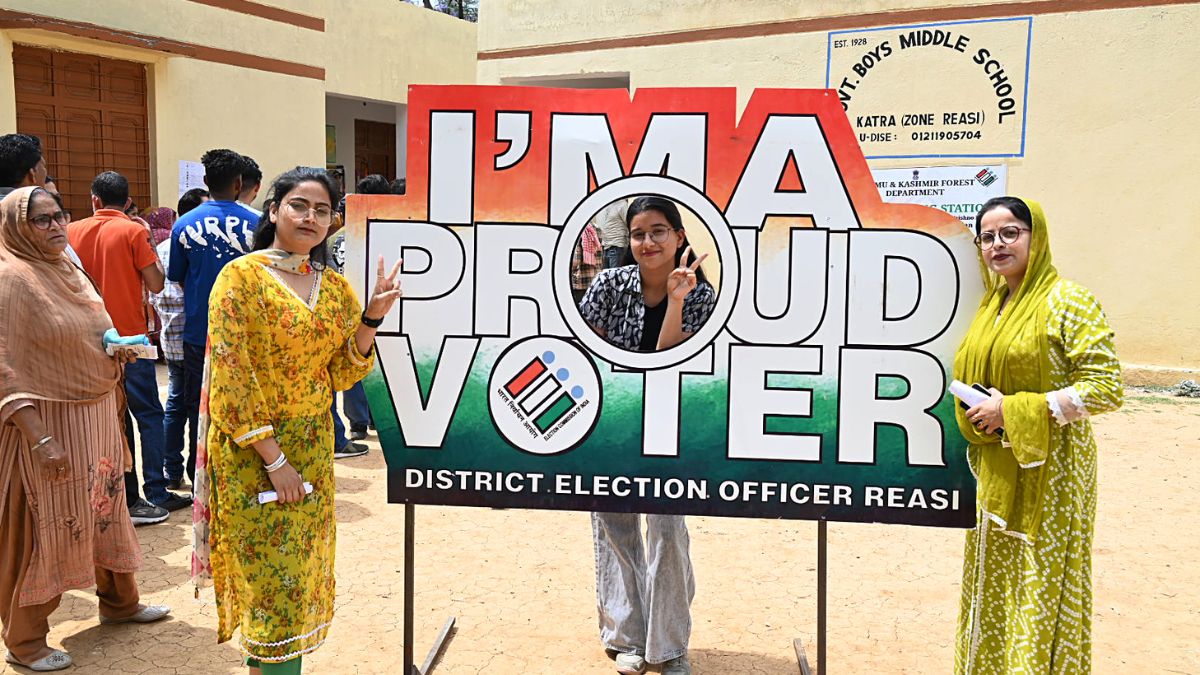
- Lok Sabha Elections
- Mera Power Vote
- Nagaland Board Result
- IPL 2024
- Live Election News
- PM Modi
- Ott Releases
- BTS
- CBSE Result
- 8 hours agoLifestyle
Keep In Mind These Expert-Recommended Do's And Don'ts To Manage Sports Injuries
- 10 hours agoLifestyle
- 1 hour agoEntertainment
Top 5 Highest-Paid Kdrama Actresses: Lee Young Ae, Lee Ji Eun, Song Hye Kyo And Others
- 2 hours agoEntertainment
Samantha Ruth Prabhu Finds Work As Mental Health Advocate Difficult: 'Not Really Easy...'
- 3 hours agoEntertainment
Parineeti Chopra Opens Up On Bollywood Nepotism And Favouritism; Says 'Priyanka And I...'
- 7 hours agoEntertainment
BLACKPINK Jennie And Zico's Spot Song Out; Lisa, Jisoo And Rose Send Love | Watch